Windows Registry Rootkit
by admin
Tuesday, January 8th, 2013 at 11:39 pm
Kernel rootkit, that lives inside the Windows registry value data and uses a buffer overflow of win32k.sys for persistance. Check it out ::HERE::
Kernel rootkit, that lives inside the Windows registry value data and uses a buffer overflow of win32k.sys for persistance. Check it out ::HERE::
While the concept on DMA through firewire isn’t new (around 2006-ish with
Winlockpwn – no longer developed.) A new project has picked up where winlockpwn left off. The newer version called Inception is able to unlock winxp,vista,7,8,osx,ubuntu,mint. It works over FireWire, Thunderbolt, ExpressCard and PCMCIA . If the machine doesnt have it you can slap one in and the driver should automatically install even though its locked. Great for bypassing machines that have encryption like bitlocker, trucrypt, etc… that are left locked. Newer version of OSX have patched this though as of Oct. 2011. I tested on Backtrack5 r3 against winxp,win7 x32, and OSX 10.7.3 and it worked like a charm.
Check it out ::HERE::
Mark Gamache posted on his blog on how he was able to break the NTLM handshake using cloudcracker.com. Check it out ::HERE::
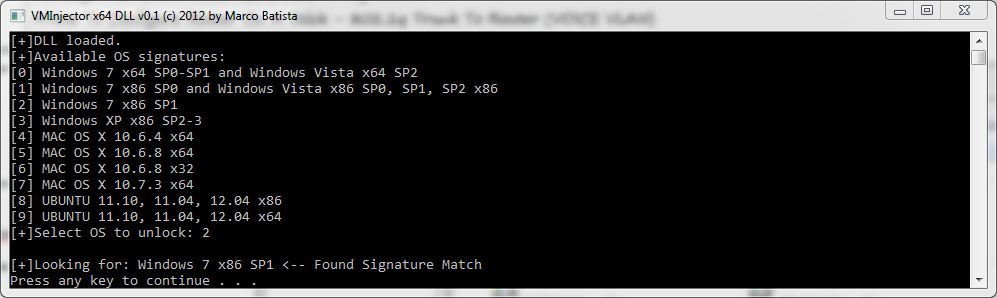
VMInjector is a tool designed to bypass OS login authentication screens of major operating systems running on VMware Workstation/Player, by using direct memory manipulation it can be used if the password of a virtual host is forgotten and requires reset. VMInjector can currently bypass locked Windows, Ubuntu and Mac OS X operation systems (x32 & x64).
You can grab a copy ::HERE::
Started working on re-adding files to the files section, this will include programs and assembly source code from our past programs. Most of our old programs will definitely be detected by antivirus so don’t be an idiot and email us saying there’s virus on the files, they are virus related obviously, the ones with included source code you would have to modify first before using. We’ve also included some programs that friends have made too that were coded in assembly.
Nick Harbour wrote on his blog about new spyware using fxsst.dll which is present on the system when the system is running as a Fax server. Seems the explorer.exe automatically loads the dll when logging on. Mubix decided to test this out with a .dll generated in Metasploit and it worked every time on his test system (WinXP) but Win7 64bit was still having issues with the dll he generated.
TL;DR – Take any malware DLL, name it fxsst.dll and drop it in C:\WINDOWS or the System32 folder and Explorer.exe will load it at boot time.