Iran so far away
by admin
Monday, April 27th, 2026 at 7:28 pm
yearly check in , still not ww3 yet though. bbl.
yearly check in , still not ww3 yet though. bbl.
OK after serious neglect for a while now i finally got around to updating some shit on the site. Still lazy and using WordPress so come hack it if you can. Discord server is still around so ping me if you want access.
now that covid is over and ww3 about to start figured id stop by and say hi.
Starting to push all code to gitlab, all the code on github will be left there but the account will be abandoned.
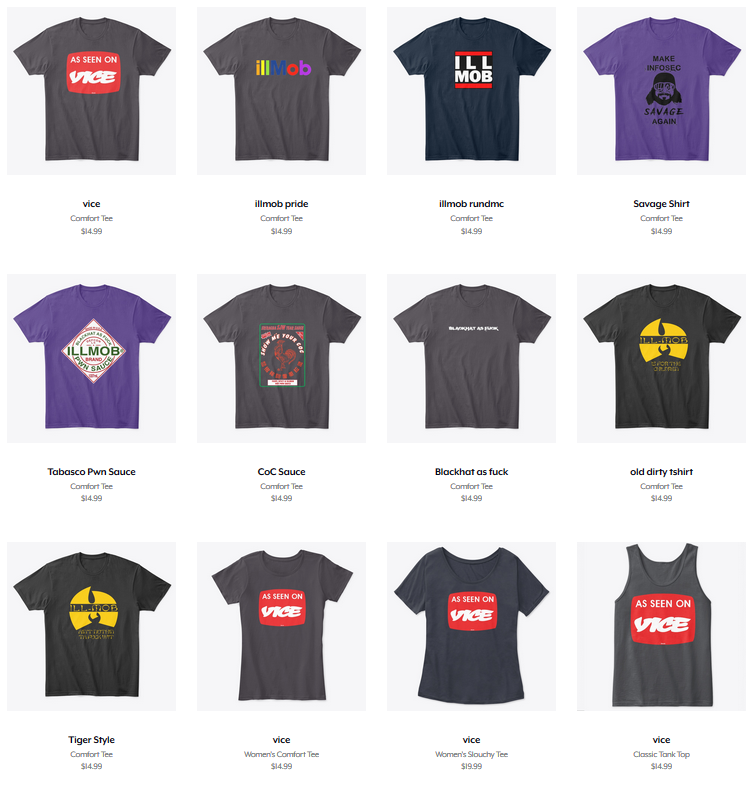
Swag reminder https://teespring.com/stores/illmob-swag-shop
Tools:
Simple tool to create HTA with Evading AV
CORS Misconfiguration Scanner.
Metasploit Shellcode Grows Up: Encrypted and Authenticated C Shells
harismuneer/Ultimate-Facebook-Scraper
Invoke-Procdump.ps1
SkelSec/pypykatz 0.3.0 released
rogerorr/DllSurrogate-dll to call x32com from x64 binaries
phackt/stager.dll- metasploit shellcode detection evasion
ANDRAX v4 DragonFly – Penetration Testing on Android
request smuggler
facebookincubator/WEASEL- DNS covert channel implant
Cobalt Strike 4.0 Released
macOS Red Team: Calling Apple APIs Without Building Binaries
antonioCoco/RogueWinRM – Windows Local Privilege Esc
xFreed0m/Disruption – Terraform script to deploy AD-based environment on Azure
b4rtik/ATPMiniDump – Evading WinDefender ATP credential-theft
sachinkamath/ntlmrecon – fast NTLM reconnaissance
Pwnagotchi 1.4.0 Released
FSecureLABS/awspx– Graph tool for access and resource relationships in AWS
https://hat.sh/
leo-lb/wpbrute-rs – WordPress login bruteforcer
CVE-2019-2890 – PoC
harleo/asnipASN – IP range attack surface mapping
Mimikatz 2.2.0 20191125 – released
hackerschoice/thc-tesla-powerwall2-hack
sailay1996/UAC_Bypass_In_The_WildWindows 10 UAC bypass for all executable files which are autoelevate true
0vercl0k/CVE-2019-11708 – Full exploit chain (CVE-2019-11708 & CVE-2019-9810) against Firefox on Windows 64-bit.
Reading:
AMSI as a Service — Automating AV Evasion
Bad Binder: Android In-The-Wild Exploit
Getting Malicious Office Documents to Fire with Protected View
Weak encryption cipher and hardcoded cryptographic keys in Fortinet products
Reflected XSS in graph.facebook.com leads to account takeover
Cracking Mifare Classic cards with Proxmark3 RDV4
Red Team Diary, Entry #3: Custom Malware Development
Evading WinDefender ATP credential-theft
Dumping LSASS without Mimikatz with MiniDumpWriteDump
[CVE-2019-14899] Inferring and hijacking VPN-tunneled TCP connections.
HackerOne breach lets outside hacker read customers’ private bug reports
your_xkcd_passwords_are_pwned
CVE-2019-12750: Symantec Endpoint Protection Local Privilege Escalation
BMW Infiltrated by Hackers Hunting for Automotive Trade Secrets
We thought they were potatoes but they were beans (from Service Accounts
Spilling Local Files via XXE When HTTP OOB Fails
Tools:
https://github.com/byt3bl33d3r/WitnessMe
https://github.com/NotSoSecure/cloud-service-enum
https://github.com/theMiddleBlue/CVE-2019-11043
https://github.com/cobbr/Covenant
https://github.com/n1xbyte/donutCS
https://sqlectron.github.io/
https://github.com/sansatart/scrapts/blob/master/shodan-favicon-hashes.csv
https://gitlab.com/initstring/evil-ssdp
https://github.com/nyxgeek/ntlmscan
https://twitter.com/cry__pto/status/1190045825914802176
https://github.com/3gstudent/Homework-of-C-Language/blob/master/Install_.Net_Framework_from_the_command_line.cpp
https://github.com/initstring/uptux
https://github.com/b4rtik/RedPeanut
https://github.com/rvazarkar/SharpHound3
https://github.com/Binject/go-donut
https://github.com/infosecn1nja/MaliciousMacroMSBuild
https://gist.github.com/TarlogicSecurity/2f221924fef8c14a1d8e29f3cb5c5c4a
https://shenaniganslabs.io/2019/11/12/Ghost-Potato.html
https://github.com/0x09AL/RdpThief
https://github.com/Mr-Un1k0d3r/SCShell
https://labs.nettitude.com/blog/introducing-sharpsocks-v2-0/
https://github.com/FuzzySecurity/Sharp-Suite#remoteviewing
https://github.com/liamg/pax
https://github.com/skelsec/jackdaw
Reading:
https://twitter.com/Alra3ees/status/1192246345341513729
https://www.mdsec.co.uk/2019/11/rdpthief-extracting-clear-text-credentials-from-remote-desktop-clients/
C2 Comparisons
https://twitter.com/OSINTtechniques/status/1197102283869376513
http://powerofcommunity.net/poc2019/Qian.pdf
https://www.nccgroup.trust/uk/about-us/newsroom-and-events/blogs/2019/november/cve-2019-1405-and-cve-2019-1322-elevation-to-system-via-the-upnp-device-host-service-and-the-update-orchestrator-service/
https://medium.com/@c2defense/man-in-the-network-network-devices-are-endpoints-too-d5bd4a279e37
https://leucosite.com/Edge-Local-File-Disclosure-and-EoP/
https://posts.specterops.io/cve-2019-12757-local-privilege-escalation-in-symantec-endpoint-protection-1f7fd5c859c6
https://www.embercybersecurity.com/blog/cve-2019-1378-exploiting-an-access-control-privilege-escalation-vulnerability-in-windows-10-update-assistant-wua
http://tpm.fail/
https://limitedresults.com/2019/11/pwn-the-esp32-forever-flash-encryption-and-sec-boot-keys-extraction/
https://www.bleepingcomputer.com/news/security/magento-urges-users-to-apply-security-update-for-rce-bug/
https://medium.com/@d.bougioukas/red-team-diary-entry-2-stealthily-backdooring-cms-through-redis-memory-space-5813c62f8add
https://medium.com/@two06/amsi-as-a-service-automating-av-evasion-2e2f54397ff9
https://googleprojectzero.blogspot.com/2019/11/bad-binder-android-in-wild-exploit.html
Breaches:
https://threatpost.com/hackers-dump-2-2m-gaming-cryptocurrency-passwords-online/150451/
https://headleaks.com/2019/11/21/millions-of-sites-using-jetpack-wordpress-plugin-exposed-by-a-security-vulnerability-Q1VaTHc4VUhUazZGeWcyWDgxL2dYQT09
https://www.helpnetsecurity.com/2019/11/20/confidential-medical-images/
https://gizmodo.com/7-5-million-adobe-accounts-exposed-by-security-blunder-1839364598
https://www.bleepingcomputer.com/news/security/macys-customer-payment-info-stolen-in-magecart-data-breach/
https://pastebin.com/8rXhtqgr
+20 new dumps added to our database
https://github.com/h43z/dns-rebinding-tool/
http://intx0x80.blogspot.com/2019/10/JWT.html
https://twitter.com/kaluche_/status/1181834267204210688
https://github.com/Hackplayers/Salsa-tools
https://github.com/AlmondOffSec/PoCs/tree/master/Windows_wermgr_eop
https://github.com/HunnicCyber/SharpSniper
https://github.com/3gstudent/GadgetToJScript
https://github.com/ZeroPointSecurity/GoldenTicket
https://github.com/coolboy4me/cve-2019-0708_bluekeep_rce
https://github.com/bugbounty-site/exploits/tree/master/CVE-2019-14994
Reading
https://xz.aliyun.com/t/6498
https://thewover.github.io/Bear-Claw/
https://blog.hunniccyber.com/phishing-with-netlify/
https://www.preempt.com/blog/drop-the-mic-2-active-directory-open-to-more-ntlm-attacks/
https://silentbreaksecurity.com/cve-2019-10617/
https://www.nextron-systems.com/2019/10/04/antivirus-event-analysis-cheat-sheet-v1-7-2/
https://jailbreak.fce365.info/Thread-It-s-possible-once-again-to-bypass-iCloud-by-using-a-CFW-with-the-CheckM8-Exploit?pid=1151#pid1151
https://offsec.almond.consulting/windows-error-reporting-arbitrary-file-move-eop.html
https://ssd-disclosure.com/archives/4033/ssd-advisory-openssh-pre-auth-xmss-integer-overflow
https://safebreach.com/Post/HP-Touchpoint-Analytics-DLL-Search-Order-Hijacking-Potential-Abuses-CVE-2019-6333
Tools:
HRShell – Flask HTTP/HTTPS Reverse Shell/C2
Evil WinRM + Donut-Loader
USB Armory MKII
PyPyKatz-WASM – Parse lsass dumps in the cloud
https://shell.now.sh/
SMB2 snapshots with Impacket SMBClient
Python API wrapper for spyse.com tools
SharpDoor – termsrv.dll multiRDP patcher
Reading:
https://thehackernews.com/2019/09/windows-fileless-malware-attack.html
https://posts.specterops.io/understanding-and-defending-against-access-token-theft-finding-alternatives-to-winlogon-exe-80696c8a73b
https://www.praetorian.com/blog/running-a-net-assembly-in-memory-with-meterpreter
Just in time for summer camp , finally got around to adding designs to new illmob store on ::teespring:: tried to keep the prices to at cost. We will also be handing out some stickers and prizes given out randomly if you find us. See you there!
