CoC
by admin
Tuesday, February 5th, 2019 at 3:20 am
TL;DR: The infosec ‘community’ is a dumpster fire. (with lots of screenshots that everyone loves to post.)
So since a shitty reporter wrote a hit piece of a one-sided view of the illmob facebook group, figured we’d get all the info on the table so you can make your own conclusions instead of following the narrative. This was never about illmob being misogynists. They wanted to twist it to make it seem like posts about the few women who caused drama and fake the funk in the scene were us including all women. Even though there was other females in the group.
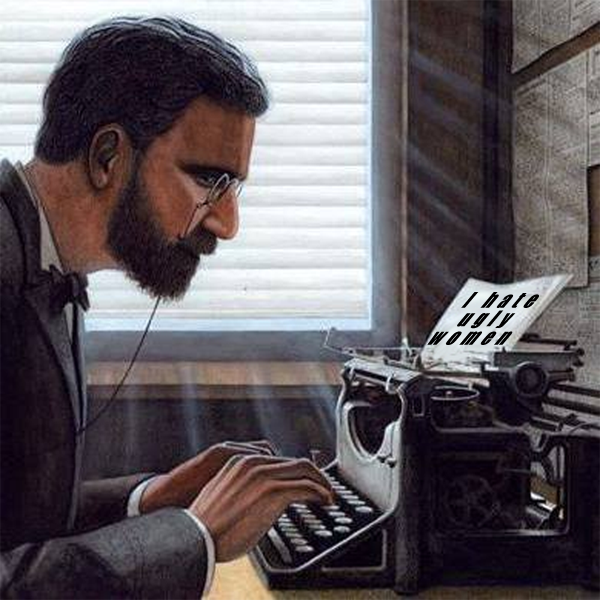
On illmob it was mostly a lot of posts related to infosec, we dropped security related news, 0days, tools, breaches and yes talked shit about people we felt cause drama or we call out for being a fraud. If this happened in 2010-2011 we would have been called racists for calling out Gregory Evans for calling himself World’s #1 Hacker.
This changed in September 2017 when tweets started popping up on Twitter about conferences adopting Codes of Conducts etc , trying to push the GamerGate narrative into the infosec community. Tweets from Roxanna ‘@theroxyd’ Dehart , who had never attended a single DerbyCon started to push the agenda of asking why the conference doesn’t have a CoC. There was some back and forth between a few of us. Including me, Martin Bos, Roxy, Brian ‘@DeviantOllam’ Rea, and Wesley Mcgrew. During the time I was making stickers and ended up making this sticker.

And I got into the back and forth fight with Wesley McGrew over the sticker which I made a photoshop of him

I was calling him out because usually the loudest backers of bullshit are the ones who want to pretend to be for the cause.
Example: This tweet about Georgia Weidman after she had posted on Twitter asking for opinions on her new website design, I said her logo was shitty

the resulting tweet a few months later was from her trying to tweet BsidesCT to try to get me removed from the conference for being mean about artwork. But it did make her improve the logo …

This started a whole pile up on Twitter of people questioning her abilities during which Georgia’s mom made an account on Twitter to fight with everyone. I got this message from Wesley:

So does this make a Wesley a misogynist because he was going against someone he felt didn’t belong, was it worse he did it in private?
Was he complacent for being in the group with a ‘burner account’

^ nuff said.
We’ll get back to Georgia further down the post…
One good thing to come out of the DerbyCoC stickers was resulting in me selling all of the stickers for donations and then donating all the funds received to 2 different non-profits that support women in technology. (Girls Who Code & CyberJutsu Girl’s Academy)


Some of the leftover funds from money coming in after DerbyCon went to the Puerto Rico Hurricane fund, which happened right around the same time.

But yea we’re a misogynist hate group…
Now let’s address this tweet. This is the tweet that set it all off. I understand relationships go bad, and can have bad actors on both sides. People can also be vindictive as fuck after breaking up. Not to say nothing happened that was tweeted, or to downplay the seriousness of the accusations, but it’s up for the police and courts to decide once all the evidence is presented from both parties. Not for Twitter or a conference to decide.

Being that I was working security for the conference, upon seeing this tweet, I had a duty to let the rest of security know about this. Because it was in a sea of other people that were already talking shit on Twitter I may have not worded it in a way that was understood by some.
Immediately I was PM’d and this conversation happened.

Hopping on our security team Slack I immediately informed the team to make sure they were aware there may be an issue and that we should look into it. She had stated there was paperwork submitted but this had not trickled down to the rest of the team. I was only trying to help, I wasn’t trying to be offensive to someone who may have experienced something like what was tweeted.
Upon coming out of that PM , I was greeted with a tweet from Brian ‘DeviantOllam’ Rea , whom I was already arguing with in previous weeks. Twitter isn’t the greatest medium to get points across because noone knows your tone or intention. Hence this response.

Im not one to take shit , especially from some no-talent assclown who does lockpicking party tricks that my locksmith down the street does daily. I responded and said I was on staff and told him to go back to being a cuck. Brian immediately called Dave at his wife’s birthday dinner to cry about being called a cuck.

This was from Dave’s own Facebook page, Dave was at dinner and didn’t want drama, so he had head of security call me to say that I couldnt’ come to Derbycon. Which of course was changed to I was able to come just not volunteer my time to do security. I wasn’t getting paid to work, I drove 12 hours each way for 7 years to help with a conference that I believed was one of the best conferences around with awesome people. I didn’t want anything in return. I vented in the illmob group at the time which alot of people were a part of at the time, including people who helped run Derbycon.
The accuser’s ex-bf also hit me up during this time

Making light of the situation during the weekend I made some photoshops to fuck with Brian ‘DeviantOllam’ Rea , which got circulated from the group of him and his wife Tarah Wheeler. There was people in the group who knew Brian and sent him screenshots. Such as the ones seen below. It’s the fucking internet, if shit like this offends you then you arent built for the internet.


We knew there was a leak because someone took a photo of them trying to laugh it off while they were at DerbyCon, pointing at the pictures. I photoshopped those out and made it them laughing at ‘her’ book. Which was also posted in the group.


During this time Shannon ‘@snubs’ Morse along with Roxy, started to chime in more with Codes of Conduct and even went as far as writing a Tumblr blog post naming me, a derbycon videographer (IronGeek), the accused/unnamed rapist , and YTCracker as ‘women haters’. It also told the story of how YT grabbed snubs ass during a drunken defcon party a few years earlier. YT admitted he was wrong and apologized profusely. I tweeted to her asking her about her grabbing Bill Gardner’s ass at DerbyCon to jump the beer line, in which I was blocked. The post was discussed in the group and with another photoshop. At some point it was discussed that she had some nude photos to her boyfriend that had got leaked, these files were easily found if you just google her name, there was no threat to release her pictures because they were already floating around the internet for more than 10 years now, we werent the ones disseminating . Does that make it right talking about it? No. But neither do false claims.

So that was post from September 2017 which Kyle ‘@eiais’ Spiers from Google , (who was in the illmob group also) started to circulate recently to make it look like the narrative we hated on ‘all’ women. These were from the discussion we had during the Derbycon CoC fiasco. He only had/screenshotted these because he was friends with Brian ‘DeviantOllam’ Rea. This wasnt because he was some sort of hero for women. Goes to show someone’s privacy ethics when friends are involved, I’m sure he fits right in with Google’s privacy policy.
That pretty much brings us to present there was two posts unrelated to the previous drama , but got intertwined into the whole DerbyCon drama in 2018. I was there this year but stayed in my room to watch most of the talks because the vibe was off and I was only there to hang out with friends.
There was a Mental Health Village to help people in the community deal with their various issues. There was a whiteboard outside the village asking “what makes you happy?” Someone wrote ‘boobies’ then someone else wrote underneath ‘#metoo’ and pointing to the writing. This caused issues with one female attendee @deborahlindseyl. She tweeted to @derbycon about the issue and was unsatisfied with the timeliness of their response. She also criticized Amanda Berlin for covering the offending text with a sticker (which also happened to be a podcast Amanda was a part of) so she accused them of trying to cover it up and promote the podcast.
She also went on to criticize Walmart Security for having mustache combs at their booth, and not anything for women. People went on to assume she was just another shit-stirrer and didn’t take her opinion that a poor attempt at a joke should be something that the conference as a whole should be responsible for. AFAIK the conference organizers tried to resolve the issue as quick as possible but I was apart of anything so I cant confirm what went down. Other people that were there did comment in the group on what went down, along with report of other people complaining that there was nazis at DerbyCon because someone was photographed doing the ‘circlegame’ symbol. After this died down someone thought it would be funny to post a picture of her face on a battleship calling her ‘BattleCunt’

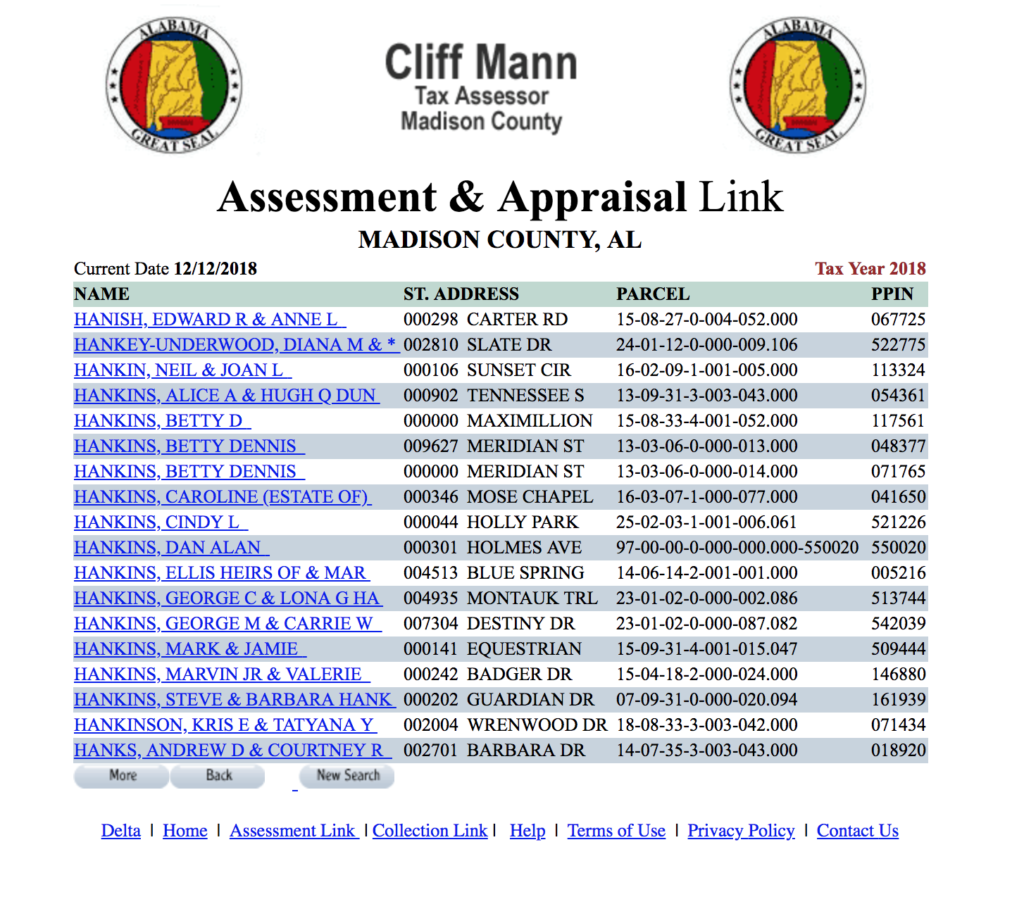
Around the same time someone posted a tweet from Georgia Weidman claiming that DerbyCon 2013 was worse that an attempted rape that happened when she and Brian ‘DeviantOllam’ Rea were attending a conference in Poland. (During which Brian didn’t believe her narration of events, in which he later apologized for 4 years later on his blog and deleted previous tweets saying she was a liar.) 
People in the thread were questioning her state during DerbyCon, where she admits to drinking before and during her talk, which wasn’t well-received. Not because she was female , it was just the content was filled with drunken ramblings. Other items from people who had in-person accounts of her doing/saying other things mentioned in the screenshots. Shit got rowdy in the posts with both men and women responding their opinion and experiences. Also there was talk that she did training while drugged up, it was so bad that conference organizers offered attendees another free class to make up for it.
Besides noone wants to take you seriously if you dress like this during a technical conference.

Georgia herself recognizes the CoC narrative

The report for Motherboard was also in the group, and had been in the group for over 18 months. He was brought into the group by Runa Sandvik who was an original illmob member. He was a tech writer so everyone figured he was there to get the latest tech scoop before other reporters did. He must have had a deadline to meet to deviate from the normal writing he did, Do I blame him for the article? Yep. It was a one-sided piece, he messaged a few people involved in the article , including me. He didn’t even take time to research anything, he went from messaging to article within the afternoon. here’s my conversation.




As you can see the shitting on males narrative doesn’t make for a good hit piece. It was poorly researched considering the length of time in the group (18months to 2 yrs), does that make him complacent like everyone that feels the need to apologize for being in the group so they don’t call their place of work trying to get them fired? We were a group of guys AND girls we didn’t hate women.
If you want to fit your own narrative of one of the players in this drama, who promotes ‘women in tech’, even wrote a book on it, is now being sued in court along with her employer for allegedly trying to force people she was in charge of to do illegal things. see ::HERE:: and ::HERE:: , trial scheduled for next year if not settled out of court beforehand. When someone complained to HR, Tarah responded by wiping evidence from one of the plaintiffs under the guise of a ‘laptop upgrade’. Shit like this in the workplace does worse for women than some Memes and name calling.
I’ll leave you with me being my ‘meanest’ on Facebook.

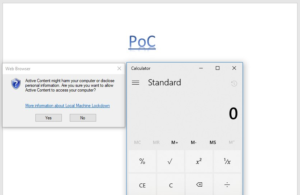
her ability as a wordpress ‘dev’ to leave .bak backup in root directory

her ability to write a ‘book’ which she relied on other women to write

Female attendee Derbycon 2017.
p.s. the Facebook group never closed, people were removed and trimmed down to less than 50 members who continue to discuss infosec and learn. fuck the bullshit.
p.s.s. for those thinking im only photoshopping women, https://imgur.com/a/28mndq2
UPDATE 9/1/2019:
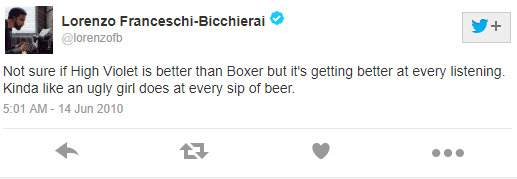
Seems like our little journalist, Lorenzo Franceschi-Bicchierai, is no stranger to being a misogynist homophobe himself. He tried to age old “sorry im ashamed of these tweet and I’ve changed” when confronted by them and then deleted the tweets. The internet is forever cupcake, nice try though.




 Skype
Skype Email
Email Keybase.io
Keybase.io

